Secure banking
even on insecure systems

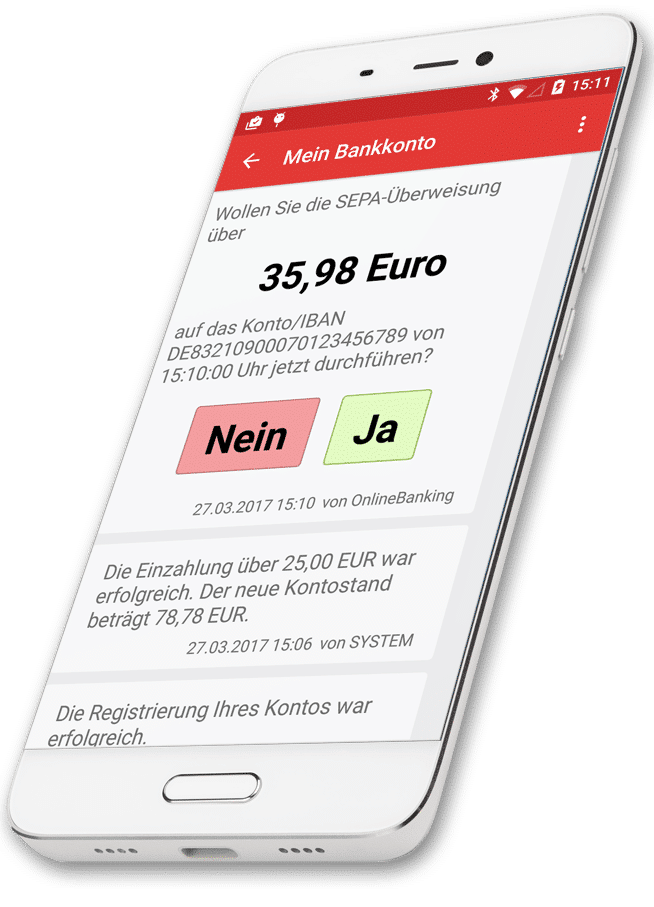
SIGN – Push & Tan services
Secure transaction authentication for smartphones and desktops – no special hardware required. SIGN supports internet TANs via push and cloud services, immediate authorisations without TANs, automatic migration of the app data onto new mobiles and authentication on smart devices. All these options for online banking and online payment transactions with credit cards, for instance.
CSF - Security Framework
The CORONIC Security Framework (CSF) protects applications and other software running on insecure IT systems. CSF hardens your software, making it resistant to hackers and Trojans. This shields your business transactions from attacks – even when working in insecure environments.
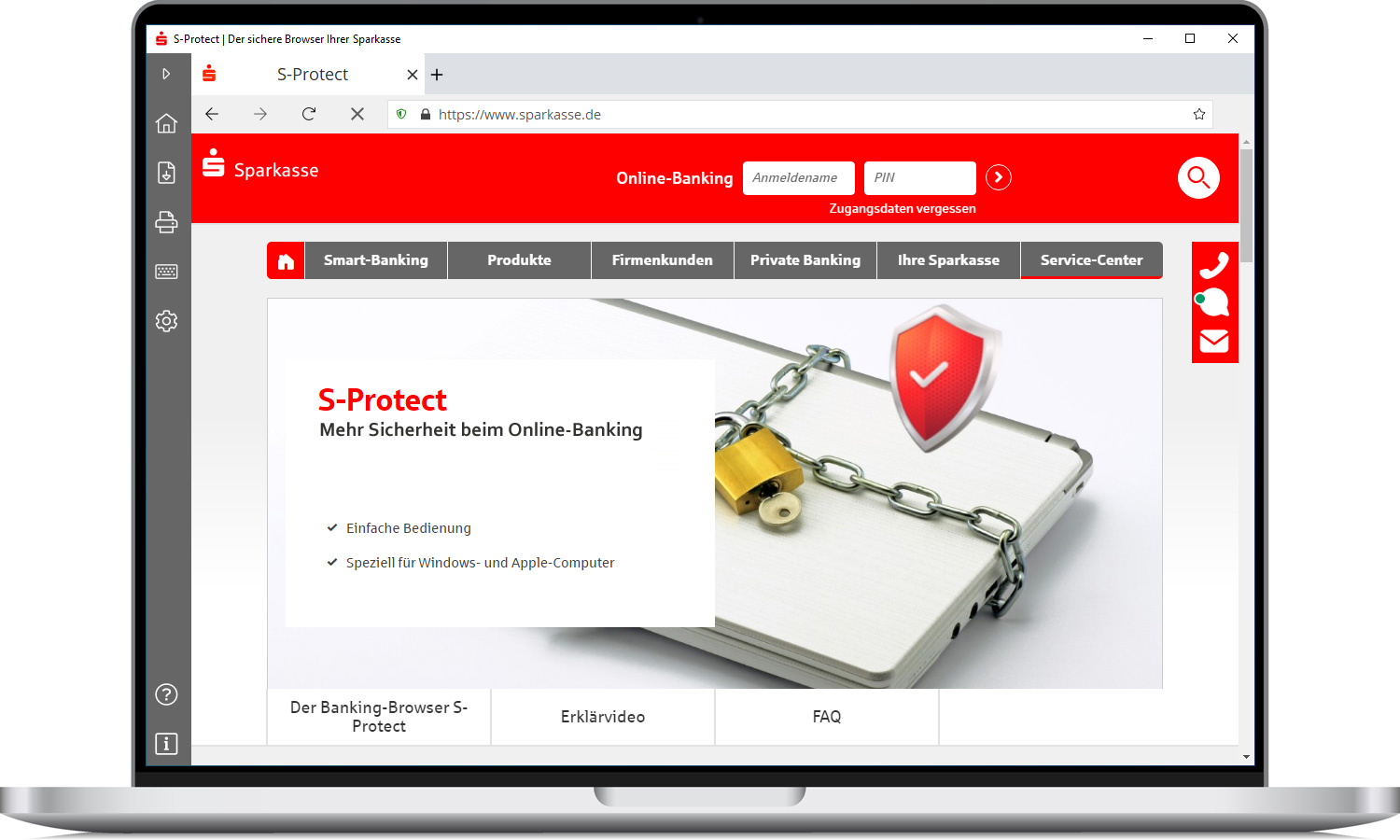
PROTECT - Hardened browser
Thanks to the PROTECT Browser, you can work on any PC or mobile device both easily and securely – even if the system is already vulnerable. Malware and hackers don’t stand a chance. Banking transactions and payments remain secure.
VISOR - Online Computercheck
The VISOR Computercheck automatically identifies security flaws on the computer and in the browser and helps clients resolve the issues. VISOR is a form of online PC and smartphone MOT for people with little technological knowledge.